Mar
Ensuring Security in API Integration: Best Protocols & Practices

In today’s digital-first world, APIs are the backbone of modern software. They enable seamless communication between applications, automate workflows, and allow businesses to leverage data across systems. However, with this connectivity comes risk. Ensuring secure API integration is critical to protect sensitive data, maintain compliance, and prevent costly breaches.
API vulnerabilities can lead to unauthorised access, data manipulation, service interruptions, and damage to brand reputation. That’s why security cannot be an afterthought it must be a core part of your API integration strategy. This blog explores key protocols, best practices, and strategies to help businesses safeguard their APIs effectively while supporting seamless operations.
Why Security in API Integration Matters
APIs often carry sensitive business and customer information, including personal data, financial transactions, and internal operational details. A breach in an API can expose these resources to malicious actors, leading to regulatory penalties, financial loss, and diminished customer trust.
Common risks of unsecured APIs include:
- Unauthorised access to sensitive data
- Data leakage or tampering
- Denial-of-service attacks that disrupt operations
- Exploitation of outdated or misconfigured endpoints
By prioritising secure API integration, organisations can prevent these risks, ensure business continuity, and provide safe digital experiences for their users. Security should be built into the design, deployment, and maintenance of APIs, creating a strong foundation for reliable and scalable integrations.
Core Principles of Secure API Integration
Successful API security starts with a clear framework and foundational principles:
- Authentication & Authorisation – Verify the identity of users and systems accessing your APIs and control what they can do. Strong authentication mechanisms, such as OAuth 2.0, JWT tokens, or API keys, ensure that only legitimate parties interact with your services.
- Data Encryption – Protect data both in transit and at rest. Use HTTPS for communication between applications and secure storage for sensitive information. Encryption ensures that even if data is intercepted, it remains unreadable to attackers.
- Rate Limiting & Throttling – Prevent abuse and system overload by limiting the number of API requests per user or client. This helps maintain performance and mitigates the risk of denial-of-service attacks.
- Regular Monitoring and Auditing – Continuous logging and monitoring of API usage help detect unusual patterns, unauthorised attempts, or performance anomalies. Regular audits identify vulnerabilities before they can be exploited.
- Minimal Data Exposure – Only share the data that is necessary for API requests. Avoid returning unnecessary sensitive information that could be exploited.
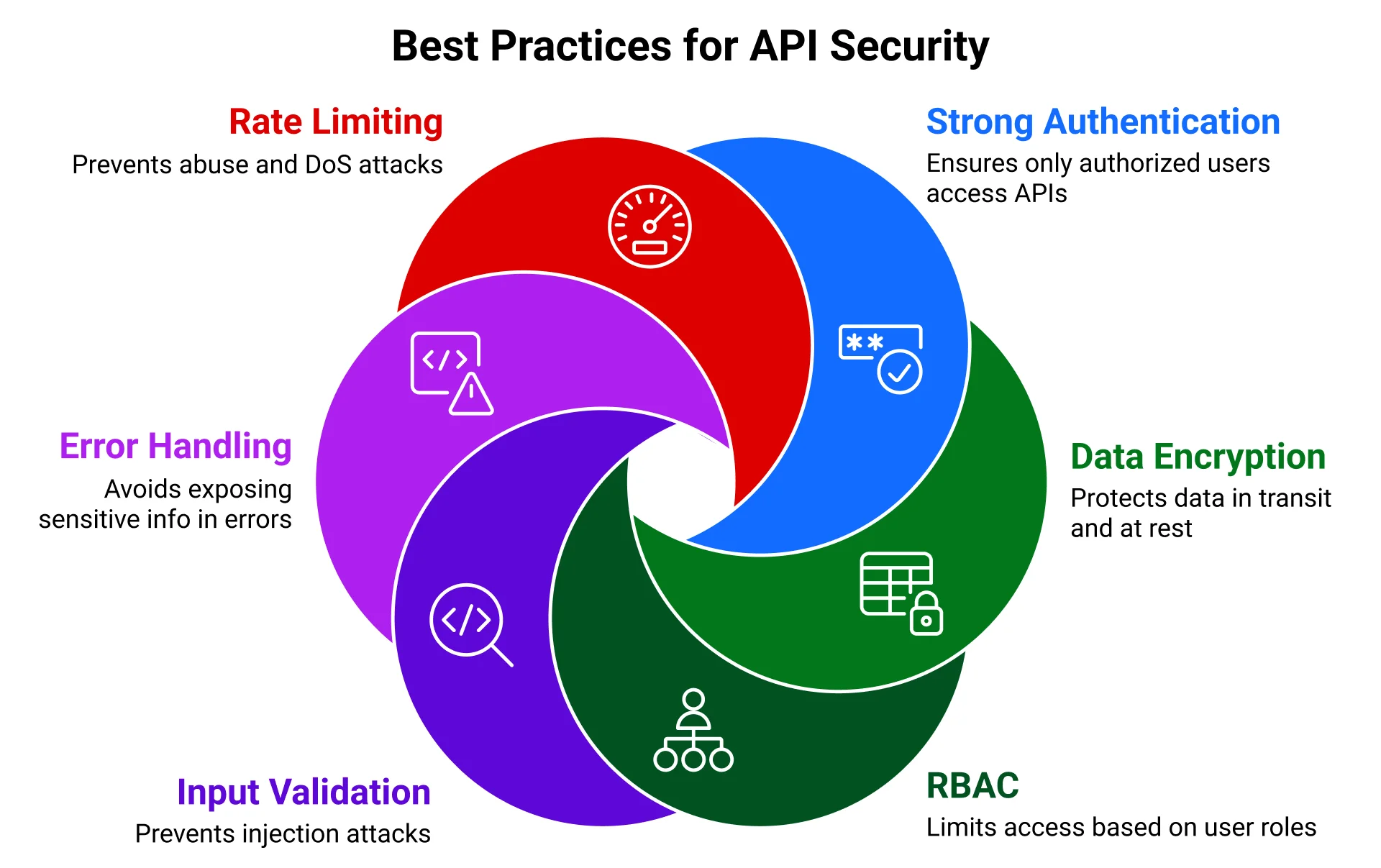
Best Practices for API Security
Implementing secure API integration requires following widely recognised API security best practices:
1. Strong Authentication Methods
Authentication is the first line of defense. OAuth 2.0, JWT, and API keys help ensure that only authorised users and applications can access your APIs. Rotate keys regularly, avoid hardcoding credentials, and enforce multi-factor authentication when appropriate.
2. Data Encryption and Secure Communication
Use HTTPS to encrypt data in transit and encrypt stored data using industry-standard algorithms. Secure communication prevents interception and tampering of sensitive information while in motion or at rest.
3. Role-Based Access Control (RBAC)
Not all users or applications need the same level of access. Define roles and permissions to limit access to critical endpoints. RBAC reduces the potential damage caused by compromised credentials.
4. Input Validation and Sanitisation
Validate all incoming requests and sanitise inputs to prevent injection attacks, such as SQL or XML injections. Proper input handling is essential for preventing attackers from exploiting API vulnerabilities.
5. Error Handling and Logging
Avoid exposing detailed internal system information in error messages. At the same time, maintain thorough logging for troubleshooting and security auditing. Proper error handling protects sensitive information while enabling operational insights.
6. Rate Limiting and Traffic Management
Apply throttling and rate-limiting policies to prevent abuse from both malicious actors and unintentional high-volume requests. These controls ensure APIs remain available under high demand while mitigating the risk of denial-of-service attacks.
Secure API Design Considerations
Security should be embedded into API design from the start. Thoughtful design reduces risk and makes maintenance easier over time:
- Versioning and Deprecation Policies – Maintain backward compatibility while retiring outdated endpoints carefully. Proper versioning reduces vulnerabilities associated with legacy APIs.
- Minimal Data Exposure – Only provide the data necessary for specific API calls to limit exposure in case of a breach.
- Consistent Security Protocols – Apply the same security protocols across all endpoints to maintain uniform protection.
- Segregation of Duties – Separate critical operations and sensitive data from non-critical functions to minimise risk exposure.
Protecting APIs from Security Threats
APIs face a variety of threats, including injection attacks, cross-site scripting, man-in-the-middle attacks, and denial-of-service attempts. Mitigating these threats requires a combination of secure design, strict protocols, and proactive monitoring.
Effective strategies include:
- Using API gateways to manage traffic and enforce security rules
- Implementing firewalls and intrusion detection systems
- Conducting automated threat detection and alerts
- Regular penetration testing to identify vulnerabilities
By combining these measures, businesses can significantly reduce the risk of attacks and maintain secure API operations.
Ongoing Maintenance and Monitoring
Security is an ongoing process, not a one-time setup. Even after implementing best practices, organisations should:
- Continuously monitor API usage and performance
- Conduct regular audits and vulnerability assessments
- Patch and update APIs and associated infrastructure
- Perform load and stress testing to ensure stability under high traffic
These continuous improvements help ensure that APIs remain secure as usage grows and threats evolve.
Future-Proofing Secure API Integration
Secure API integration should also consider long-term growth and adaptability. Future-proofing strategies include:
- Designing modular APIs that can scale independently
- Implementing cloud-based infrastructure for dynamic resource allocation
- Establishing comprehensive monitoring and alerting systems
- Documenting security protocols for developers and teams
By planning for growth while maintaining rigorous security practices, businesses can build APIs that are both scalable and resilient.
Conclusion
Ensuring secure API integration is essential for modern businesses that rely on interconnected systems and data-driven workflows. By adopting API security best practices, implementing strong protocols, designing APIs with security in mind, and maintaining continuous monitoring, organisations can protect sensitive information, prevent breaches, and deliver reliable services.
Ficode Technologies specialises in delivering secure and scalable API integration services. Our team implements proven security protocols, robust authentication, and continuous monitoring to help businesses safeguard their APIs while enabling seamless, future-ready operations.