Apr
Why API Security is Critical for Modern Web Applications

You have been coding for a while. You have built some APIs, connected a few services, maybe even pushed something to production. But did you ever stop and think that my API actually secure?
Most developers assume API security is someone else’s problem, it is not. If you built the API, keeping it safe is on you. And the good news? Most API attacks are not complicated. They happen because of small, simple mistakes that are easy to fix once you know about them.
What Is API Security?
An API is how two systems talk to each other. Your app talks to your server through one. Your server talks to a payment gateway through one. Every modern web application runs on APIs in the background.
Web API security means making sure the wrong people cannot get in, mess with your data, or access things they should not.
Think of it like a debit card. The ATM only works if you have the right card and the right PIN. Get either one wrong and you are not getting in. API security works the same way – it checks who you are before it lets you do anything.
API Security Risks You Actually Need to Know
Most API vulnerabilities come from the same basic mistakes. These are among the most referenced issues in the OWASP API Security Top 10 – and the five you will run into most often in real-world development.
1. Weak Authentication
If your tokens never expire or your API keys are sitting in a URL, attackers can grab them and use them forever. Always set an expiry time on your tokens.
2. Missing Ownership Checks
A user is logged in and sees their order at /api/orders/1234. They change it to /api/orders/1235 and get someone else’s order. Your API checked that they were logged in – but never checked if that order was theirs. Always check both.
3. Excessive Data Exposure
Your API returns everything – password, balance, admin flag and hopes the frontend hides the sensitive bits. Attackers do not use your frontend. They call the API directly and see all of it. Only return what is needed.
4. No Rate Limiting in APIs
No limits means a bot can hammer your login page thousands of times, try every password, or crash your server with too many requests. A simple rate limit stops all of that.
5. Insecure Configuration
Leaving debug mode enabled or exposing stack traces in production gives attackers valuable insights. These configuration mistakes can lead to serious security breaches.
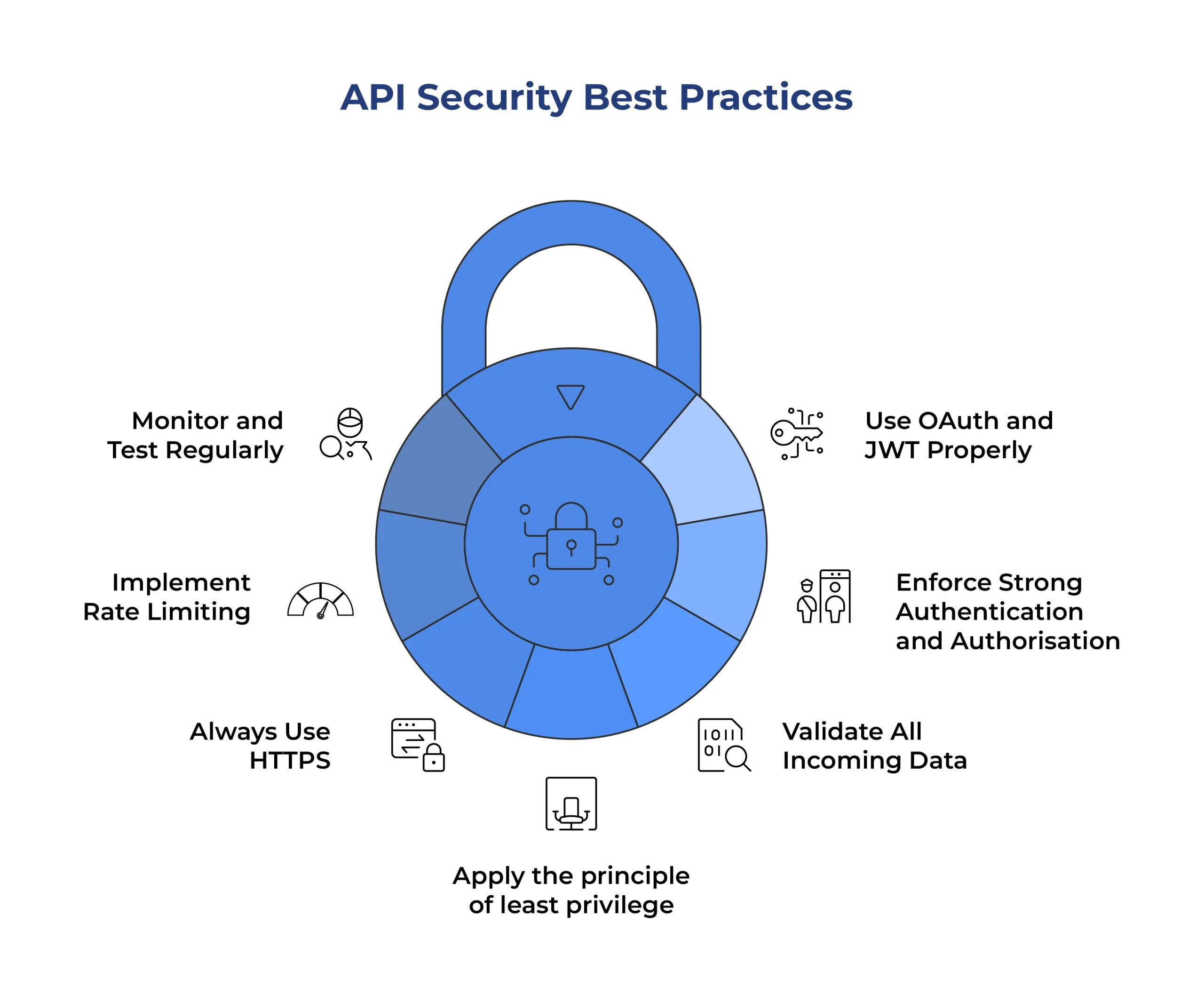
API Security Best Practices That Work
To protect your application from common threats, follow these essential API security best practices:
1. Use OAuth and JWT Properly
Set an expiry time on every token and check it on every request – not just at login. Do not store tokens in local storage. If a token gets stolen and never expires, the attacker has access forever.
2. Enforce Strong Authentication and Authorisation
Being logged in is not enough, you also need to check that the record belongs to them. Add that ownership check inside your route handler. One missing check is all it takes.
3. Validate All Incoming Data
Always check what is coming in – type, length, and format on the server side. Keep your error messages vague so you do not give away useful information. Never show a stack trace in a response.
4. Apply the principle of least privilege
Every API user, service, and token should only have access to exactly what they need – nothing more. If a service only reads data, it should not have write permissions. If a token is scoped to one endpoint, it should not work on others. The principle of least privilege sounds simple, but it significantly reduces the blast radius when something does go wrong.
5. Always Use HTTPS
HTTPS encrypts everything moving between your client and server. Use TLS 1.2 or higher (preferably TLS 1.3) to ensure secure communication between client and server.
6. Implement Rate Limiting
Apply rate limiting in APIs at the gateway level to control traffic. Be stricter on sensitive endpoints such as login and password reset.
7. Monitor and Test Regularly
Run security checks whenever your API changes. Monitor unusual patterns such as repeated failed logins or suspicious request behaviour to detect threats early.
Conclusion
API security sounds like a big topic, but most of the problems come down to a short list of API security risks that are completely avoidable. Tokens that do not expire. Data returned to anyone who asks. No limits on how many requests someone can make. Missing ownership checks on records. None of these require expert-level knowledge to fix.
The key is not advanced techniques, but consistent habits. Build security into every step – validate inputs, control access, and return only what is necessary. These fundamentals form the backbone of every secure API.
You don’t need to know everything to get started – you just need to prioritise security from the beginning.
At Ficode, we help businesses design and develop secure, scalable digital solutions with security built in from the start. If you are looking to strengthen your APIs or build secure web applications, our team can help.